August 15, 2024
What Is Passwordless Authentication? Benefits, Challenges, Implementation

Passwords are becoming a thing of the past as more individuals and companies are moving towards passwordless security. With passwordless authentication, users can access their accounts without having to remember and input long, complex passwords. This method not only simplifies the login process but also increases security by reducing the risk of password-related cyber threats. Let’s dive into what passwordless authentication entails and explore how it can benefit you and your business.
The Problem With Passwords

Attackers can use brute force methods to generate random username/password combinations. They exploit common weak passwords like “123456” or use specialized software to continuously try different combinations until the correct one is found. This method is hard to prevent if users are using weak or easily guessed passwords.
Credential Stuffing
If your password is stolen on one account and you’re using the same username/password combination on different accounts, attackers can use these credentials to gain access to multiple accounts of yours. This type of attack can be challenging to detect, especially if attackers use stolen credentials a few weeks or months after obtaining them.
Phishing
Phishing attacks involve sending fake emails or text messages to trick users into giving up their login credentials. These messages often appear to come from a legitimate source, like a bank or social media company, and contain a link to a fake login page. Once users enter their information, attackers can steal it and log in to their accounts.
Keylogging
Keyloggers are a form of malware that can be installed on your computer without your knowledge. These programs capture every keystroke you make, including your usernames and passwords when you log in to websites. Keyloggers are difficult to detect and can record vast amounts of sensitive information over time.
Man-in-the-Middle Attacks
Man-in-the-middle attacks involve intercepting communications between a user and a server. Attackers can insert themselves between the two parties and observe the data being sent back and forth. If the user is entering login credentials during this time, the attacker can record them and use them to access the user’s account later on.
Related Reading
What Is Passwordless Authentication?
Passwordless authentication is a method of verifying a user’s identity without the need for passwords. Instead, individuals provide alternative forms of evidence such as biometrics, hardware tokens, or one-time codes. This approach enhances security by reducing the risk associated with stolen or weak passwords, enhancing the user experience, and lowering IT costs and complexity.
Enhancing Security with Anonybit’s Decentralized Biometrics Authentication
At Anonybit, we help companies to prevent data breaches and account takeover fraud with our decentralized biometrics system design. With decentralized biometrics solution, companies can enablepasswordless login,, wire verification, step-up authentication, and help desk authentication. We are on a mission to protect companies from data breaches, account takeover and synthetic identity fraud. .
To achieve this goal, we offer security solutions such as:
- Secure storage of biometrics and PII data
- Support for the entire user lifecycle
- 1:1 biometric authentication and 1:N biometric matching for to prevent duplicates, synthetics and blocklisted identities
Anonybit eliminates the tradeoffs between privacy and security. Prevent data breaches, enable strong authentication for eliminating account takeovers, and enhance the user experience across the enterprise using Anonybit.
Book a free demo today to learn more about our integrated identity management platform.
What Are The Types Of Passwordless Authentication?

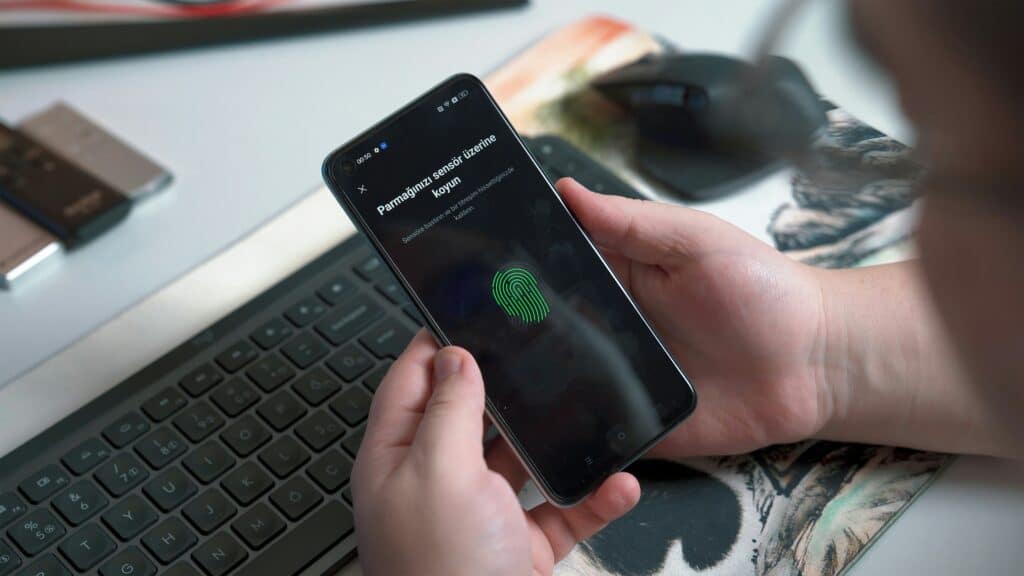
Biometrics is one of the most fascinating ways to authenticate a user without resorting to passwords. It can leverage physical traits like selfies, palm prints, fingerprints, iris scans, and other physical and behavioral traits to uniquely identify a person.
Modern AI may have made it easier for hackers to spoof certain physical traits, advanced liveness detection techniques make it possible to discern presentation attacks, deepfakes and injection attacks.. This makes biometrics one of the most secure passwordless authentication methods available today.
Possession Factors: Authentication via Ownership or Possession of a Device
Possession factors leverage something that a user owns or carries with them to authenticate them. For instance, a smartphone authenticator app can generate a code that the user needs to input in order to access a system. Similarly, OTPs (One Time Passwords) can be sent to the user via SMS for verification. Even hardware tokens can be used to authenticate a user without the need for passwords.
Magic Links: Email-based Authentication
Magic links are a more user-friendly way of authenticating a user without passwords. Here, the user simply enters their email address, and the system sends them an email containing a secure link. When the user clicks on this link, they are granted access to the system. It is a simple and effective way that can be used to authenticate users without the need for remembering passwords.
Why Should You Use Passwordless Authentication?
Passwordless authentication makes life easier as you do not need to remember different passwords anymore.
Passwordless authentication takes the frustration out of the equation to create a better consumer experience. It improves consumer experience, particularly mobile applications because users only need an email address or mobile phone number to sign up.
Related Reading
- Enterprise Authentication
- Passwordless Authentication Methods
- U2F Vs FIDO2
- Azure Ad Passwordless
- Passwordless Technology
- FIDO Standard Security Key
- Is Passwordless Authentication Safe
- FIDO2 Passwordless Authentication
- Implementing Passwordless Authentication
- Passwordless Authentication Examples
- Passwordless Multi Factor Authentication
- Benefits of Passwordless Authentication
- Passwordless SSO
- Passwordless vs MFA
- How To Implement Passwordless Authentication
- Common Authentication Vulnerabilities
- Passwordless Authentication UX
- Passwordless Authentication Benefits
How Does Passwordless Authentication Work?

Passwordless authentication is an innovative authentication method that enhances security and user experience in various ways. This method essentially eliminates the need for traditional passwords, thereby enabling users to log in to websites and services securely without the need to remember complex combinations of characters.
Instead of relying on passwords, passwordless authentication leverages various alternative factors to verify that a person is who they claim to be. These factors can include biometrics like fingerprint or facial recognition, one-time passwords (OTPs) sent via email or SMS, hardware tokens, or authentication through social media accounts. Biometrics are by far the most secure form of passwordless authentication.
The process of passwordless authentication typically involves the following steps:
1. User Initiation
When a user attempts to log in, they are redirected to the login page, where they can select the passwordless login option.
2. Identity Verification
The user’s identity is then verified through one of the alternative factors they choose, such as a biometric or an OTP sent to their registered email address or phone number.
3. Authentication
Once the user’s identity is confirmed, they are granted access to their account or the requested service without having to input a traditional password.
By eliminating passwords, passwordless authentication minimizes the risk of security breaches due to weak or reused passwords. It simplifies the login and identity verification process for users, reducing the chances of forgotten passwords and streamlining the overall user experience.
Strengthening Security Measures with Anonybit’s Biometric Solutions
At Anonybit, we help companies prevent data breaches and account takeover fraud with our decentralized biometrics technology features. With our decentralized biometrics, companies can enable passwordless login, wire verification, step-up authentication, and help desk authentication and more.
To achieve this goal, we offer security solutions such as:
- Secure storage of biometrics and PII data
- Support for the entire user lifecycle
- 1:1 authentication and 1:N matching for lookups and deduplication.
Anonybit eliminates the tradeoffs between privacy and security. Prevent data breaches, reduce account takeover fraud, and enhance the user experience across the enterprise using Anonybit.
Book a free demo today to learn more about our integrated identity management platform.
Challenges Associated With Passwordless Authentication
- Passwordless authentication can be more complex or expensive than using passwords. These systems are still relatively uncommon and may require outside services to function.
- Biometric authentication cannot be reset. While it is relatively simple to change a password or certificate, it is impossible to change a person’s fingerprint or face if these were to be compromised. Hence secure storage of biometric data is critical.
- Passwordless authentication usually requires a secure channel during setup. Secrets are often exchanged during the setup process. If these were to be leaked, it could compromise the security of the system. For example, during the setup of TOTPs, the security token needs to be shared. If this were to be leaked, an attacker could create their own TOTP.
- OTPs can be intercepted or stolen if users’ email accounts are hacked or if their phone numbers are stolen.
Best Practices For Implementing Passwordless Authentication
One of the most important best practices when implementing a passwordless authentication system is to encourage user adoption. This can be achieved by providing plenty of resources such as user guides, training modules, and one-on-one assistance from your security team to help users become comfortable with the new system. Incentives such as gift cards or bonuses can motivate employees to complete training sessions and fully adopt the new authentication process. The fact is, when given the option, a majority of users will opt for biometrics because of their convenience.
Testing and Adoption Strategies for Passwordless Authentication
Another best practice is to take advantage of trials and beta programs to test out specific passwordless products and see how well employees adapt to the change. It’s essential to include both users and the IT department in the decision-making process to obtain feedback and thoughts on the company’s courses of action. Since these are the personnel who will be using and managing the solution, their input is invaluable.
Ensuring Successful Implementation of Passwordless Authentication
As the passwordless authentication platforms are rolled out, it is important to keep enforcement high with top-down commitment from executives and procedural changes that constantly require verification for systems. This helps ensure that the new system is used correctly and consistently throughout the organization. By following these best practices, you can help ensure that your passwordless authentication system is successful and well-adopted by users.
Related Reading
- Zero Trust Passwordless
- Passwordless Authentication Best Practices
- Passwordless Customer Authentication
- Passwordless Authentication Solutions
- Passwordless Authentication Companies
- Best Passwordless Authentication
Book A Free Demo To Learn More About Our Integrated Identity Management Platform
At Anonybit, we help companies prevent data breaches and account takeover fraud with our decentralized biometrics technology. With our decentralized biometrics framework, companies can enable passwordless login, wire verification, step-up authentication, help desk authentication and more.
Comprehensive Security Solutions for Companies
We are on a mission to protect companies from data breaches, account takeover and synthetic identity on the rise, privacy regulations, digital transformation. To achieve this goal, we offer security solutions such as:
- Secure storage of biometrics and PII data
- Support for the entire user lifecycle
- 1:1 authentication and 1:N matching for lookups and deduplication
Balancing Privacy and Security with Anonybit’s Integrated Platform
Anonybit eliminates the tradeoffs between privacy and security. Prevent data breaches, reduce account takeover fraud, and enhance the user experience across the enterprise using Anonybit. Book a free demo today to learn more about our integrated identity management platform.
