January 18, 2023
Passwordless Authentication Best Practices For A More Secure Login

In the digital age, Passwordless Security and Authentication are vital. Today’s blog will cover Passwordless Authentication Best Practices and how you can implement these strategies to safeguard sensitive data. Incorporating these reliable techniques can bolster your cybersecurity measures and safeguard your accounts from potential threats. Let’s dive in and explore how you can prioritize security while streamlining the user login experience.
Benefits Of Going Passwordless
When it comes to passwordless authentication, the benefits are numerous and clear. Firstly, this authentication type helps mitigate common cyber threats such as phishing, credential stuffing, brute force algorithms, and keylogging. These attacks rely on the threat actor acquiring login credentials like a password. An organization’s security posture is significantly strengthened by eliminating the need for passwords. There is a clear and apparent reason why 92% of businesses believe going passwordless is the future of system-access security — the benefits outweigh the costs.
Enhancing User Experience with Passwordless Authentication
Another crucial advantage of passwordless authentication is the elimination of password fatigue and the higher susceptibility to negligent password management, which results from the numerous best practices individuals must follow for secure password management. This solution drastically enhances the user experience, particularly when paired with passwordless Single Sign-On (SSO).
Financial Benefits of Adopting Passwordless Authentication
From a financial perspective, passwordless authentication is advantageous in terms of direct and indirect costs. Since no password management is required, organizations can save money by avoiding investments in password management software and frequent security training on password design and storage. IT management resources are freed from enforcing company-wide password policies, monitoring anomalous password shares, or resetting forgotten login credentials. An organization can save an estimated $1.9 million by transitioning to passwordless authentication.
Related Reading
Common Methods Of Passwordless Authentication
1. One-Time Passwords (OTPs)
One-time passwords are time-sensitive, single-use codes sent to a user’s device, adding an extra layer of security beyond static passwords. These codes are easy to implement across various platforms. However, OTPs are vulnerable to interception through phishing attacks, malware, or man-in-the-middle attacks. They also depend on the user’s mobile device or email access.
2. Hardware Tokens
Hardware Tokens provide a physical token that generates a time-based code, offering strong security independent of the network. These tokens are ideal for environments requiring high security. Yet, they can be lost, damaged, or stolen, leading to potential access issues. They are costly to distribute and manage on a large scale.
3. SMS-based Authentication
SMS-based Authentication sends a code to the user’s mobile phone, making it convenient as it does not require additional apps or devices. This method is widely supported and easy to use. However, it is susceptible to SIM swapping, interception, and other forms of SMS hijacking. It also relies on the availability of a mobile network, which might not always be reliable.
4. Push Notifications
Push Notifications send a real-time alert to the user’s mobile device for authentication approval. This method is user-friendly and provides immediate feedback on login attempts. However, it requires an internet connection and a smartphone, which may not be practical for all users. This can lead to notification fatigue, where users might inadvertently approve malicious requests.
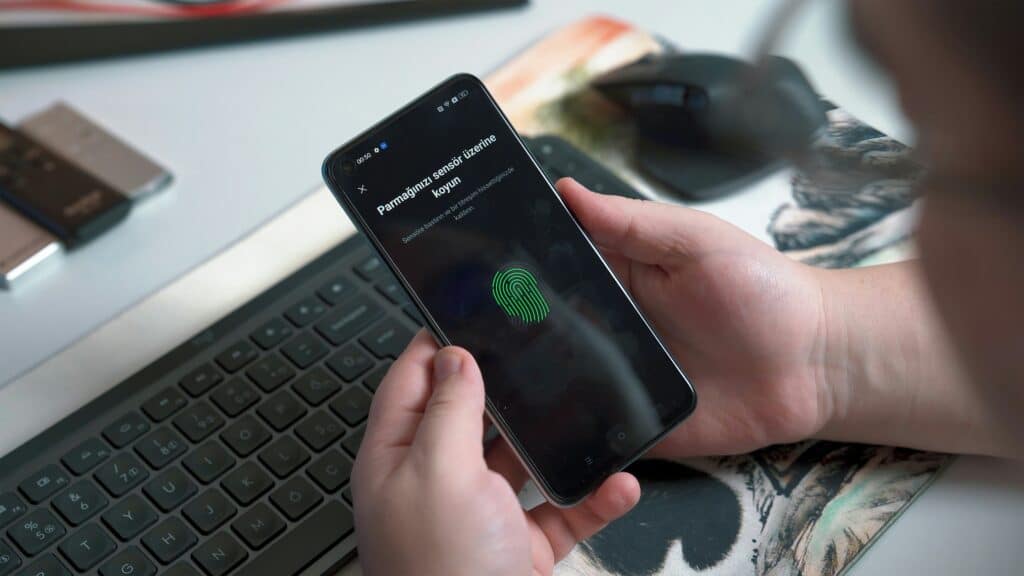
5. Biometrics: The True Passwordless Solution
While the other methods of passwordless authentication offer improved security compared to passwords, they are not entirely unphishable. Methods like magic links, pins, or codes can still be hacked using techniques like SIM swapping.
Biometrics, such as fingerprint scans, selfies, and palms, offer a genuinely passwordless experience by leveraging unique physical characteristics that are difficult to replicate or steal. Users merely present their biometric trait to authenticate, eliminating the need for any passwords or codes. This method enhances security while providing a seamless user experience, embodying passwordless authentication’s essence.
Preventing Data Breaches with Decentralized Biometric Solutions
At Anonybit, we help companies prevent data breaches and account takeover fraud with our decentralized biometrics system design. With a decentralized biometrics solution, companies can enable passwordless login, wire verification, step-up authentication, and help desk authentication. We are on a mission to protect companies from data breaches, account takeover and synthetic identity fraud.
To achieve this goal, we offer security solutions such as:
- Secure storage of biometrics and PII data
- Support for the entire user lifecycle
- 1:1 biometric authentication and 1:N biometric matching to prevent duplicates, synthetics and blocklisted identities
Anonybit eliminates the tradeoffs between privacy and security. Prevent data breaches, enable strong authentication for eliminating account takeovers, and enhance the user experience across the enterprise using Anonybit.
Book a free demo today to learn more about our integrated identity management platform.
Passwordless Authentication Best Practices For A More Secure Login

Implement Strong Authentication with Biometrics
Biometric systems, such as fingerprint scanners and selfies, use unique physical traits to authenticate users. These traits are extremely difficult to replicate, making it challenging for unauthorized users to gain access. Biometric data is unique to each individual, offering a high level of security. Advanced biometric systems can also detect spoofing attempts, adding a layer of protection against fraud.
Utilize Multi-Factor Authentication (MFA)
MFA combines multiple authentication methods, such as biometrics and hardware tokens. This ensures that if one factor is compromised, the other remains a barrier. By requiring multiple forms of verification, MFA significantly reduces the likelihood of unauthorized access, especially if biometrics are one of the factors. Even if a hacker obtains one factor, they still need to bypass the additional layers of security.
Secure Enrollment Processes
Implementing rigorous identity verification during enrollment prevents unauthorized individuals from registering their credentials. This might involve in-person verification or using a trusted third-party service. Securing the initial setup ensures that only legitimate users can register their biometrics or devices. This step is crucial for preventing fraudulent enrollments and maintaining the integrity of the authentication system.
Regularly Update and Patch Systems
Keeping biometric authentication software up-to-date with the latest security patches addresses vulnerabilities and protects against new threats. Regular system updates and patches are essential. Regular updates ensure that any discovered vulnerabilities are promptly fixed, preventing potential exploitation. This practice keeps the authentication system robust against evolving security threats.
Educate Users
It is vital to provide users with training on how to securely use passwordless authentication methods. Education should include best practices for device and data security. Educated users are less likely to fall victim to phishing or other social engineering attacks. Understanding the importance of securing their devices and data helps users contribute to the overall security of the authentication system.
Monitor and Audit Access
Implement continuous monitoring and regular audits of authentication logs to detect unusual or suspicious activity. This involves analyzing access patterns and promptly responding to anomalies. Ongoing monitoring and auditing help identify and address security incidents quickly. By detecting suspicious activity early, organizations can prevent breaches and ensure the integrity of their authentication processes.
Implement Secure Biometric Data Storage
Biometric data should be stored securely using encryption and other data protection measures. Instead of storing raw biometric data, use technology like Anonybit’s, which leverages multi-party computing and zero-knowledge proofs to break down the biometric data into anonymized pieces.
The pieces (or anonybits) are not only secured individually over a decentralized network but they are matched in a distributed way as well. Thisensures the security of the biometric data at rest and in process, preventing unauthorized access and exploitation. Storing the biometric data in this way ensures that even if it is compromised, it remains unreadable and unusable by attackers.
Related Reading
- Enterprise Authentication
- Passwordless Authentication Methods
- U2F Vs FIDO2
- Azure Ad Passwordless
- Passwordless Technology
- FIDO Standard Security Key
- Is Passwordless Authentication Safe
- FIDO2 Passwordless Authentication
- Implementing Passwordless Authentication
- Passwordless Authentication Examples
- Passwordless Multi Factor Authentication
- Benefits of Passwordless Authentication
- Passwordless SSO
- Passwordless vs MFA
- How To Implement Passwordless Authentication
- Common Authentication Vulnerabilities
- Passwordless Authentication UX
- Passwordless Authentication Benefits
Challenges Of Passwordless Authentication
Cost
The initial costs of implementing passwordless authentication can be a barrier for some organizations. While the long-term benefits are attractive, the upfront expenses for purchasing necessary hardware (required for fingerprint and palm) and software are burdensome. Incorporating this solution into an existing tech stack service can be a lengthy and complex process, adding to the implementation costs.
Training
The shift to passwordless authentication can pose challenges, especially for end-users. Employees are accustomed to using usernames and passwords for accessing applications, which would change with this new solution. Adequate training is essential for both users and help desk staff who will manage it.
Access
From a security standpoint, there are a few limitations depending on the method of passwordless authentication. For example, if an employee used a push notification to their phone or a hardware token to verify their identity and lost their phone or token, they wouldn’t be able to gain access. It also becomes a problem if a hardware authenticator is lost or stolen.
For these access reasons, biometric authentication methods like selfies or palms are highly favored in passwordless authentication since they are nearly impossible to phish.
Related Reading
- Zero Trust Passwordless
- Passwordless Customer Authentication
- Passwordless Authentication Solutions
- Passwordless Authentication Companies
- Best Passwordless Authentication
Book A Free Demo To Learn More About Our Integrated Identity Management Platform
Anonybit offers a decentralized biometrics feature that helps companies prevent data breaches and account takeover fraud. By utilizing passwordless authentication with decentralized biometrics, companies can implement several security measures, including passwordless login, wire verification, step-up authentication, and help desk authentication.
With these features, Anonybit is committed to protecting companies from the increasing threats of data breaches, account takeovers, and synthetic identity issues. In light of the evolving landscape of privacy regulations and digital transformations, Anonybit provides:
- Secure storage of biometrics and personally identifiable information (PII) data
- Support for the entire user lifecycle
- 1:1 and 1:N matching for lookups and deduplication
Through its innovative offerings, Anonybit effectively eliminates the traditional trade-offs between privacy and security, enabling companies to prevent data breaches, strengthen authentication to combat account takeovers and improve the overall user experience across various enterprise platforms.
Book a free demo today to explore the capabilities of Anonybit’s integrated identity management platform and bolster your company’s security protocols.


