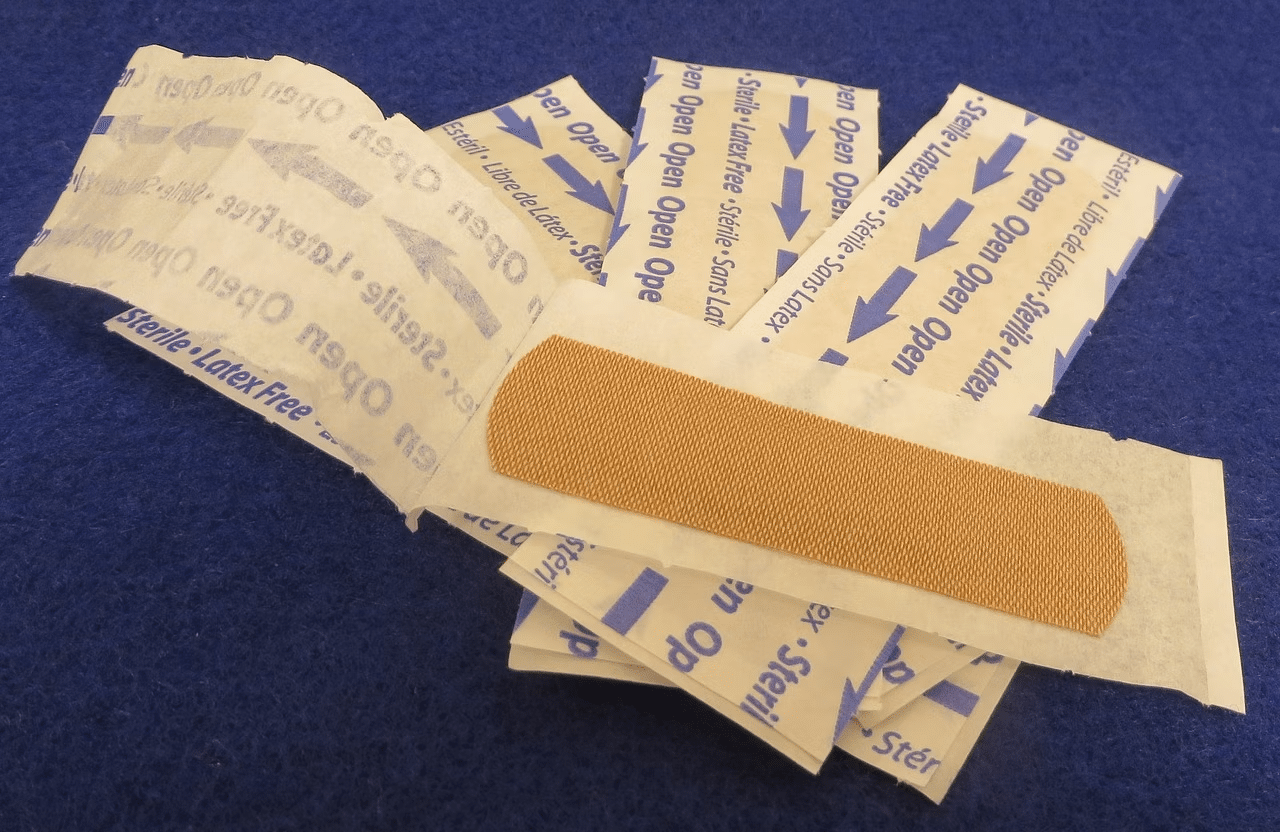
In an increasingly digital world, identity management has become a fundamental concern. Whether it’s accessing your email, banking online, or simply logging into your favorite social media platform, proving your identity is a daily necessity. Yet, enterprises struggle with the ever-increasing complexity of technology and the relentless persistence of cyber threats. In fact, despite advances in technology and a growing awareness of the importance of cybersecurity, the current state of identity management often resembles a patchwork of bandaids, where numerous solutions and technologies attempt to address the issue but often fall short of providing a comprehensive and secure system.
Before delving into the bandaids, challenges it is important to put into context how fundamental identity management is to the way we as a society operate today. Our lives are only becoming more and more entwined with digital platforms, from work to social interactions to obtaining government services, healthcare, gaming, and more. Identity management isn’t just about creating and remembering passwords; it’s about safeguarding sensitive information, ensuring privacy, and preventing cyberattacks.
Why Are There So Many Bandaids in Identity Management
Legacy Systems and Outdated Software: One of the major contributors to the cybersecurity patchwork is the prevalence of legacy systems and outdated software. Many organizations continue to rely on older technology that may not receive regular updates and security patches, and that cannot easily be incorporated into more modern identity orchestration frameworks. This leaves vulnerabilities unaddressed, providing cybercriminals with easy entry points.
Complexity Breeds Vulnerability: The complexity of modern IT environments is both a blessing and a curse. While technology advancements have enabled businesses to become more efficient and innovative, they have also created a sprawling and intricate web of interconnected systems. Each component in this complex ecosystem represents a potential attack vector. Managing and securing this complexity is a Herculean task, often leading to a fragmented approach to cybersecurity and identity management.
Compliance vs. Security: In many cases, organizations prioritize compliance over true security. While compliance standards are essential for setting baseline security requirements, they can sometimes lead to a checkbox mentality. Organizations may focus on meeting compliance requirements without adequately addressing the evolving threat landscape, resulting in a false sense of security.
Bandaid Solutions and Reactive Measures: In response to cyber threats and data breaches, organizations often adopt a reactive approach by applying “bandaid” solutions. This means addressing each new threat or incident as it arises rather than proactively building a robust and holistic cybersecurity and identity management strategy. While these quick fixes may provide temporary relief, they contribute to the patchwork nature of identity management, leaving the next set of vulnerabilities unaddressed until they are exploited.
The Different Bandaids in Identity Management
Passwords and Password Managers: The use of passwords remains one of the most common methods for authentication, mostly because they are easy to use and at this point, are built in to almost all application frameworks, making them hard to get rid of without serious effort. However, relying solely on passwords is problematic for all the reasons practitioners are aware of – vulnerability to breaches and users’ difficulty in creating and remembering complex passwords (multiple surveys confirm that more than 65% of people reuse the same password or version thereof, and that the most popular password by far continues to be “password”. Password managers help to some extent, but they are still part of a fragmented system, and even they too have been compromised.
Two-Factor Authentication (2FA): 2FA has become a standard security practice to enhance authentication, often involving something you know (password) and something you have (a device or code). While 2FA strengthens security, its implementation varies widely across platforms, leading to inconsistencies and user confusion. For many years already, NIST has not recommended 2FA using SMS because of all kinds of vulnerabilities (see our related blog on this topic, Getting Past the Pitfalls of One-Time Passwords).
Device Biometrics: As discussed at length on this blog, the FIDO Alliance has done a great job in promoting the use of device-based biometrics (FaceID and TouchID) as a way to get to a passwordless world. The way FIDO works is based on the biometric that is stored on a specific device protected by special hardware elements. Matching to the biometric that is stored on the device releases a cryptographic key that communicates with a server that then allows entry into the application or account, etc. In this way, FIDO supposedly achieves 2FA based on strong authentication – “something-you-have”, the device and “something-you-are”, the biometric. The problem with this approach is that there is no way to know “who” is behind the device and oftentimes the device is not linked to the original account registration. This approach also presents limitations in shared device scenarios, such as kiosks, and is especially vulnerable to account recovery attacks. In addition, more recently, researchers have exposed vulnerabilities in the storage mechanism of biometrics on the devices, managing to extract stored fingerprints on Android smartphones using a $15 circuit board. Perhaps today this is an outlier edge-case scenario, we can and should expect more and more attempts to compromise biometrics stored on smartphones as device-based biometrics become more prevalent.
Single Sign-On (SSO) Solutions: SSO solutions aim to simplify authentication by allowing users to access multiple services with a single set of credentials. If those credentials are compromised (and as discussed above they are usually based on passwords and OTP/2FA), then all of the services connected to those credentials are also compromised. The same applies to social login which may seem to be super convenient, but these third-parties are notorious for lackadaisical identity management.
Verifiable Credentials and Digital IDs: Blockchain-based identity solutions promise enhanced security and user control over personal information and greater privacy but they too are at risk of becoming yet another bandaid, as they are generally not tied into the overall identity management framework of an enterprise and generally also don’t have a robust account recovery mechanism that leaves room for attackers to exploit. This was evidenced in a recent fraud case in Louisiana where a man has been sentenced to provision for using a state authorized digital driver’s license to defraud credit unions and banks. This example specifically shows how deploying point solutions without thinking about holistic security can backfire.
No More Bandaids
Many of the identity management challenges that we face today are rooted in the desire to balance security with user privacy and user experience. To do identity management properly traditional requires the collection and storage of vast amounts of personal data, which are prone to breaches.
To address the current patchwork of bandaids, there is a growing need for a unified and holistic approach to identity management. Here are some steps towards achieving this:
- Leverage Privacy Enhancing Technologies: Using new Privacy Enhancing Technologies (PETs) like Zero-Knowledge Proofs and Multi-Party Computation, it is possible to fully protect and secure personal data of all types, including biometrics, transaction data, health data and other sensitive information that enterprises need to store and manage on behalf of their clients and employees to deliver services, etc.
- Unify the Identity Management Lifecycle: Today, to piece together a connected technology stack that covers all these elements, enterprises essentially must combine different endpoint solutions and platforms – can be up to 8-12 vendor integrations per use case! – that address each of these stages, creating enormous inefficiencies and gaps that attackers exploit. Integrated Identity Platforms (IIPs) can unify these 3 aspects of the lifecycle by storing personal data, particularly a biometric (selfie, voice, etc.) collected at the onboarding stage, binding different attributes to the biometric record, and making that biometric record available for authentication and account recovery. This means that users can access multiple applications with a consistent, persistent biometric, streamlining authentication, reducing the reliance on passwords and sharing identity information across different services, which minimizes redundant protocols and system design. By maintaining a single source of truth in an organization via an IIP, identity governance is also much more robust and easier to manage with respect to privacy and data protection regulations.
- View compliance as a starting point and not the endpoint of cybersecurity efforts. Many regulations focus on fines and high level requirements as opposed to guidelines for preventing data breaches and securing identity in the first place.
- Think like a fraudster. Human error remains a significant factor in cybersecurity breaches. Phishing attacks, social engineering, and weak passwords continue to be successful tactics for cybercriminals. It is absolutely necessary to get away from passwords and to implement biometric authentication for strong security.
Conclusion
Identity management today resembles a patchwork of bandaids, with various solutions attempting to address the complex issue of authentication and privacy. While these solutions offer some level of security and convenience, they often lack cohesion and consistency. To build a more secure and user-friendly identity management system, it is essential for organizations to rip off the bandaids and confront identity management as a user-centric, privacy-centric, strategic imperative. Only then can we move towards a more seamless and secure digital identity landscape.
To speak with industry experts and develop a “No More Bandaids” approach for your organization, click here.
