4 Ways to Safeguard Your Credit Union Members From Fraud
Credit unions, with their member-focused approach and community-oriented services, have become increasingly popular. However, they face unique challenges when it comes...
Platform Capabilities
Digital Onboarding
Prevent duplicates, manage blocklists and run velocity checks.
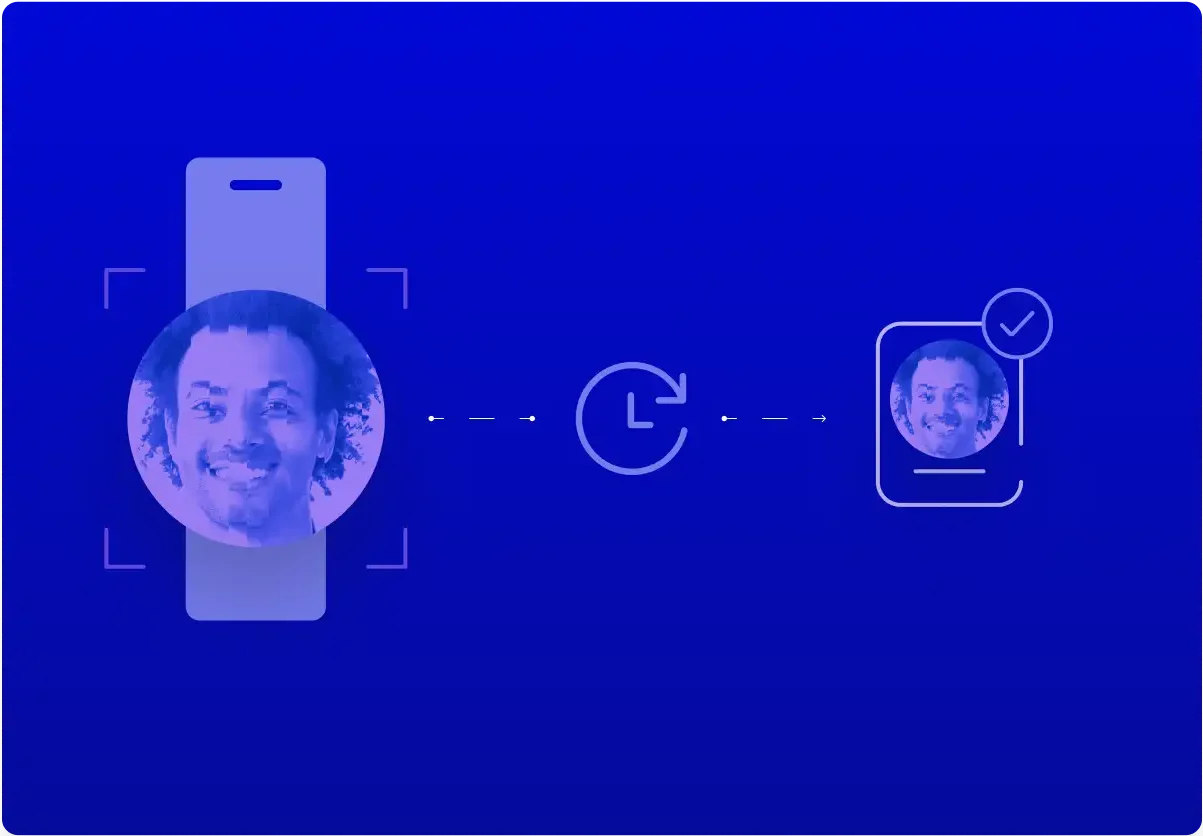
Binding
Tie digital interactions to a trusted, persistent identity.
Passwordless Authentication
Eliminate passwords with enterprise-grade authentication powered by deepfake protection, multi-modal biometrics, and 99.999% accuracy.
Account Recovery
Close the help desk gap, stop social engineering and SIM-swap attacks.
How Anonybit Works
Secure Data Storage
Safely store and manage biometrics and other sensitive data to support many enterprise use cases.
Deduplication & Blocklist Checks
Search for duplicates, synthetics and blocked identities in account opening and prevent fraud downstream.
Passwordless Login
Close the gaps in your IAM solution and extend your FIDO implementation so your enterprise is truly passwordless.
Step Up Authentication
Use biometrics instead of weak authenticators to ensure that someone is who they claim to be at the most critical points.
Contact Center Authentication
Lower AHTs, reduce fraud and enhance the caller experience at the help desk with seamless biometric authentication.
Q2 Authentication & Fraud Prevention
Harness the power of Anonybit directly within the Q2 Digital Banking Platform
Banks & Credit Unions
Strengthen bank security by closing the circle of identity with our decentralized biometrics powered platform.
Fintechs
Ensure a stellar fintech journey without compromising on security.
Retail & Hospitality
Unleash powerful customer experiences online, in-store and in between with privacy and security in mind.
Healthcare
Preserve the highest levels of patient data security with privacy-enhancing biometric authentication.
Gaming
Introduce a new era of gaming where privacy and security meet performance.

Insurance
Revolutionize insurance with cutting-edge privacy and security solutions, delivering unmatched trust and data protection.
Gig Economy
Set your gigging site apart with an elevated experience that protects buyer and seller privacy.
Telecommunications
Prevent SIM swap fraud and enable quick account access with strong authentication built on a privacy-first foundation.
Enterprise
Reduce the risk of data breaches and ransomware attacks with a biometric authentication solution that covers you from the desktop to the help desk.
Government
Propel identity management processes and secure backend personal data repositories with our decentralized backend.


Safeguarding sensitive data is more critical than ever. Data Protection Officers play a pivotal role in ensuring the privacy and security of valuable information within organizations. When it comes to choosing a reliable ally in digital security, Anonybit stands out as the ultimate choice for those in a data protection officer role who are committed to maintaining the highest standards of enterprise data protection. With Anonybit, eliminate centralized repositories of sensitive data and digital assets and give attackers nothing to find and nothing to steal.

"Rank One is excited to be partnering with Anonybit on their privacy-by-design, data sharding architecture that decentralizes the storage of biometric PII and greatly reduces the potential for future data breaches like the one that impacted OPM several years ago. We look forward to working with Frances and her team to push this important initiative forward.”
Scott Swann CEO, Rank One
Our decentralized enterprise data protection infrastructure is crafted to address a wide range of enterprise needs. The decentralized biometric cloud handles any kind of structured or unstructured data sets for maximum utility in the enterprise.
Our simple APIs make the adoption process smooth for DPOs and others in the data protection officer role. The flexible architecture is compatible with a wide range of cloud providers, orchestration platforms and existing applications, allowing you to focus on strategic initiatives rather than grappling with integration challenges.
Navigating the complex landscape of enterprise data protection requirements can be daunting. Anonybit enhances organizations’ compliance posture with GDPR, CPRA, etc. and reduces concerns around storing and managing biometrics and other sensitive data.
Stay ahead of the curve with Anonybit’s privacy by design framework and commitment to innovation. With unique capabilities around storing images, tokens and other PII, Anonybit’s decentralized data vault makes your biometric deployments future-proof, so anyone in the data protection officer role can keep up with the latest technological advances and regulatory changes.
Digital onboarding
Binding
Authentication
Account recovery
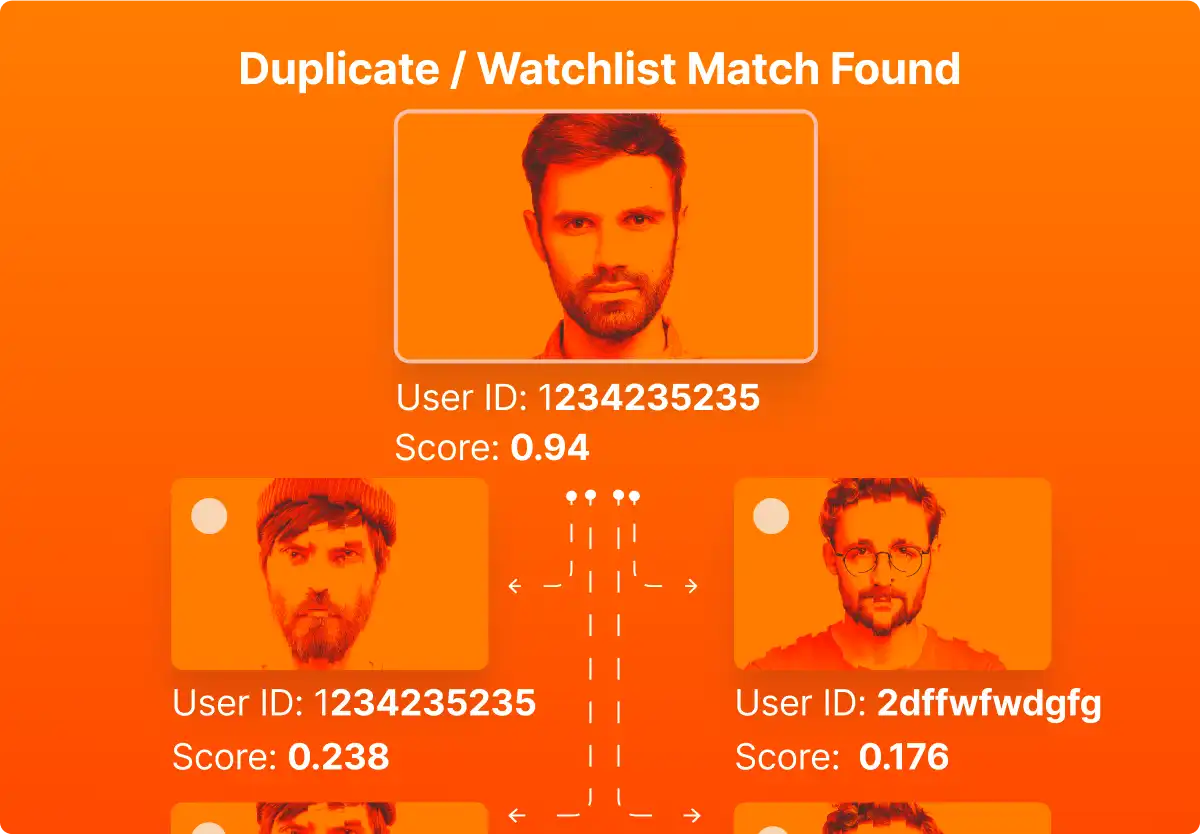
Securely store and manage biometrics and other PII collected in the onboarding process, and run a 1:N selfie check to prevent duplicates and synthetic identities.

Link devices, tokens, PassKeys and other credentials to the enrolled profile in the decentralized biometric cloud.

Leverage the biometric enrolled in digital onboarding with the second factor bound to the profile for strong identity validation and enterprise data protection.
Device-independent workflows to retrieve PassKeys and other assets stored in the decentralized data vault.
RESOURCES

Credit unions, with their member-focused approach and community-oriented services, have become increasingly popular. However, they face unique challenges when it comes...

On July 6, Marriott, the multinational hotel franchise, announced a second staggering data breach since just the beginning of this year....

Identity theft and credit card fraud are two interconnected phenomena that have become prevalent in our digital age. Criminals exploit vulnerabilities...
Get rid of central honeypots of data. Embrace biometrics across the user lifecycle.