May 03, 2024
How Does Passwordless Authentication Work & Why It’s So Important

What Is Passwordless Authentication?
Passwordless security and passwordless authentication is a verification method in which a user gains access to a network, application, or system without a knowledge-based factor such as a password, security question, or PIN. Rather than using a set of information for authentication, the user would provide something they possess, such as biometric evidence or a piece of hardware.
The Rise of Passwordless Authentication as an Identity Verification Solution
Passwordless authentication provides organizations and IT management teams with an alternative solution for identity verification because of the security and user-friendliness of its process. It’s generally used with other authentication processes such as MFA or single sign-on (SSO) and is becoming an increasingly popular substitute to the traditional username and password methods.
Addressing the Security Risks of Traditional Passwords
Passwords haven’t been safe for a long time. They are hard to remember and easy to misplace. They are also the number one target of cybercriminals. So much so that 80% of breaches involve weak or stolen passwords.
Enhanced Security and User Experience
Passwordless authentication offers a more secure and user-friendly method of accessing systems and applications. By eliminating the need for passwords, a significant security risk is removed. Passwords are often the weakest link in a security system, as they are susceptible to being stolen, guessed, or forgotten, leading to unauthorized access. In contrast, passwordless authentication methods such as biometrics are unique to the individual, making it much harder for cybercriminals to compromise. Users no longer have to remember complex passwords or change them regularly, reducing the likelihood of human error leading to security breaches.
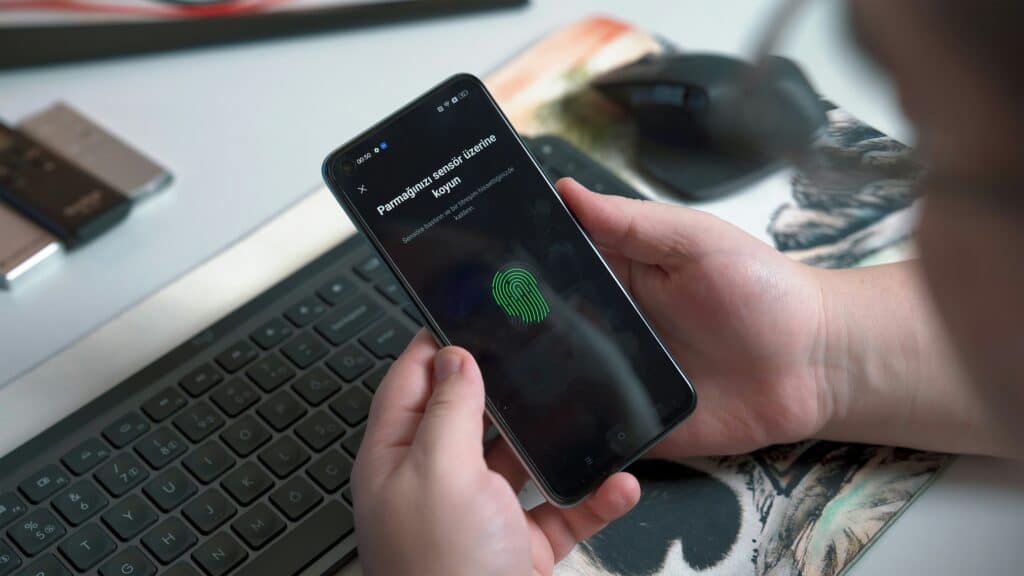
Biometric Authentication
Biometric authentication is a form of passwordless authentication that uses unique physical characteristics such as fingerprints, facial features, or retina scans to verify a user’s identity. Biometric data is difficult to replicate, making it a highly secure method of authentication.
By scanning a fingerprint or capturing a facial image, the system can compare the biometric data to previously stored information to grant or deny access. Biometric authentication offers a high level of security and convenience, as users do not need to remember passwords or carry physical tokens for authentication.
Token-Based Authentication
Token-based authentication is another form of passwordless authentication that uses a physical device or token to verify a user’s identity. This token could be a USB key, a smart card, or a mobile device that generates a one-time passcode.
The user presents the token to the system, which then validates the token and grants access if the verification is successful. Token-based authentication is highly secure, as the physical token is difficult to replicate, and access is granted only when the token is physically present.
Push Notifications
Push notifications are a passwordless authentication method that sends a notification to the user’s registered device when access is requested. The user can then approve or deny the access request directly from the notification, eliminating the need to enter a password.
Push notifications offer a convenient and secure way to authenticate users, as they rely on the user’s mobile device for verification. If an unauthorized access attempt is made, the user can quickly deny the request from their device, preventing unauthorized access.
Implementing Passwordless Authentication
Organizations looking to implement passwordless authentication should consider the security implications and user experience of the chosen method. While passwordless authentication offers enhanced security and convenience, it is essential to select a method that aligns with the organization’s security requirements and user preferences.
By adopting passwordless authentication, organizations can improve the overall security posture and user experience while reducing the risk of security breaches associated with traditional password-based authentication methods.
Related Reading
What Are The Types Of Passwordless Authentication?

Biometrics
Biometrics uses unique physical or behavioral traits to authenticate a user. This can include fingerprint or retina scans, typing dynamics, or even touchscreen dynamics. While it’s possible to fool certain physical traits with AI, it remains extremely difficult to fake behavioral characteristics.
Possession Factors
Authentication via possession factors involves something that a user owns or carries. For example, this could be a code generated by a smartphone authenticator app, one-time passwords received via SMS, or a hardware token.
Magic Links
With magic links, users simply enter their email address. The system then sends them an email containing a link. Once clicked, the link grants the user access.
Empowering Companies with Decentralized Biometrics for Enhanced Security
At Anonybit, we help companies prevent data breaches and account takeover fraud with our decentralized biometrics features. With our passwordless authentication with decentralized biometrics, companies can leverage biometrics for login, wire verification, step-up authentication, and help desk authentication and other similar use cases.
Enhancing Security with Biometric and PII Data Protection
We are on a mission to protect companies from data breaches, account takeover and fraud. Biometrics are the only way to achieve this as they are the only way to bind a person to their identity and be sure that someone is who they claim to be. Beyond passwordless authentication, our security solution also supports:
- Secure storage of biometrics and PII data
- 1:N matching for blocklist checks, synthetic identity checks and deduplication
- Integration to digital onboarding solutions as well as a variety of orchestration platforms
Balancing Privacy and Security with Anonybit’s Identity Management Platform
With its decentralized infrastructure design, the Anonybit Genie is unique in its ability to eliminate the tradeoffs between privacy and security. Prevent data breaches, enable strong authentication, eliminate account takeovers, and enhance the user experience across the enterprise using Anonybit. Book a free demo today to learn more about our integrated identity management platform.
How Does Passwordless Authentication Work?

Passwordless authentication works by replacing passwords with other authentication factors that are intrinsically safer. Instead of a user-provided password matched against what is stored in the database, passwordless systems use various methods to authenticate users securely.
Possession-based Authentication
Possession-based factors like OTPs are referred to as “something you own”. They authenticate users through device ownership by proving exclusive access to a certain device associated with a specific phone number, for example. While possession-based factors like OTPs are widely used, they are vulnerable to phishing and social engineering.
Inherence-based Authentication
Inherence-based factors such as biometrics are referred to as “something you are”. These factors involve asserting a physical or behavioral characteristic like facial recognition or fingerprint scans to authenticate users. This method provides a higher level of security compared to possession-based authentication.
Knowledge-based Authentication
Knowledge-based authentication typically involves passwords or secret answers like first pet names or mother’s maiden names. These are not considered strong authenticators today given the proliferation of data breaches and the availability of personal information for sale on the dark web.
FIDO
FIDO authentication relies on cryptographic key pairs with a private and public key. The private key is stored on the user’s device and generally can onlyaccessed through another authentication factor like a fingerprint or PIN. The public key is provided to the system for secure account access. This method of passwordless authentication has a lot of promise but it falls short in determining who is the person authenticating through the device.
Different from Auto-filling Passwords
It’s important to note that passwordless authentication differs from auto-filling passwords or using a cellphone unlock code to fill in password fields. True passwordless authentication bypasses the need for passwords altogether by using different secure technology and authentication methods.
Related Reading
- Enterprise Authentication
- Passwordless Authentication Methods
- U2F Vs FIDO2
- Azure Ad Passwordless
- Passwordless Technology
- FIDO Standard Security Key
- Is Passwordless Authentication Safe
- FIDO2 Passwordless Authentication
- Implementing Passwordless Authentication
- Passwordless Authentication Examples
- Passwordless Multi Factor Authentication
- Benefits of Passwordless Authentication
- Passwordless SSO
- Passwordless vs MFA
- How To Implement Passwordless Authentication
- Common Authentication Vulnerabilities
- Passwordless Authentication UX
- Passwordless Authentication Benefits
What Are The Benefits Of Passwordless Authentication?

There is a clear and apparent reason why 92% of businesses believe going passwordless is the future of system-access security — the benefits outweigh the costs. While passwords, in theory, seem like a constructive layer for securing organizational data and applications, they actually lead to additional access points to be exploited by cybercriminals and are expensive to maintain and support.
Enhancing Security Through Passwordless Authentication
For instance, common attacks such as phishing, credential stuffing, brute force algorithms, and keylogging only work on the premise that the threat actor can first acquire the login credentials like a password or other piece of information — then use that to access a valuable technology asset or data system. By going passwordless, you eliminate that whole component of the equation and strengthen your security posture.
Addressing Password Fatigue with Passwordless Solutions
Much of the vulnerability of passwords is tied to the tedious process employees need to undergo for secure password management. To be effective, they must follow certain best practices for designing, storing, updating, and sharing their infinite number of account passwords.
All of these strict parameters lead to password fatigue and a higher susceptibility to negligent password management. In addition, resetting passwords also typically involves knowledge questions which are easily circumvented. Using biometrics eliminates this problem and improves the overall user experience.
Is Passwordless Authentication Safe?

Passwordless authentication is often safer than traditional password-based systems for several reasons.
- It eliminates the risk of password-related breaches. With passwordless authentication, there’s no password for hackers to steal. This significantly reduces the risk of account takeover attacks, where a hacker gains access to a user’s account by cracking their password.
- Passwordless authentication typically involves multi-factor authentication (MFA). This means that even if a hacker somehow intercepts the authentication code, they would still need the other factors to gain access. This multi-layered approach significantly increases the security of the system.
- Passwordless authentication is more user-friendly. While this may sound unrelated to security, it encourages better security practices. Users are more likely to use a secure system if it’s easy and convenient for them.
In contrast, if a system is cumbersome or difficult to use, users may resort to insecure practices. This is the case today, as users commonly use weak passwords or reuse passwords across multiple accounts.
Related Reading
- Zero Trust Passwordless
- Passwordless Authentication Best Practices
- Passwordless Customer Authentication
- Passwordless Authentication Solutions
- Passwordless Authentication Companies
- Best Passwordless Authentication
Book A Free Demo To Learn More About Our Integrated Identity Management Platform
At Anonybit, we help companies prevent data breaches and account takeover fraud with our decentralized biometrics features. With our passwordless authentication with decentralized biometrics, companies can leverage biometrics for login feature, wire verification, step-up authentication, and help desk authentication and other similar use cases.
Enhancing Security with Biometric and PII Data Protection
We are on a mission to protect companies from data breaches, account takeover and fraud. Biometrics are the only way to achieve this as they are the only way to bind a person to their identity and be sure that someone is who they claim to be. Beyond passwordless authentication, our security solution also supports:
- Secure storage of biometrics and PII data
- 1:N matching for blocklist checks, synthetic identity checks and deduplication
- Integration to digital onboarding solutions as well as a variety of orchestration platforms
Balancing Privacy and Security with Anonybit’s Identity Management Platform
With its decentralized infrastructure design, the Anonybit Genie is unique in its ability to eliminate the tradeoffs between privacy and security. Prevent data breaches, enable strong authentication, eliminate account takeovers, and enhance the user experience across the enterprise using Anonybit. Book a free demo today to learn more about our integrated identity management platform.
