October 18, 2021
3 min read
Closing the Circle of Identity:
Protecting Personal Privacy Without Compromising the Convenience and Security
Let’s say you want to open a bank account remotely because, after all, it’s more convenient. It’s usually as simple as providing your driver’s license; taking a picture; and waiting for the bank to check these documents and ask you to create a username and password. After getting approved and routinely opting for FaceID on your mobile device to invoke the password that lets you in, you have unfettered access to your bank account. It’s so easy and convenient. But in reality, your bank has no way to tell if the person with the mobile device is the same person that opened the account with them remotely, and hackers knowingly exploit this by contacting the banking institution, telling a representative that they got a new phone, and providing stolen information in order to impersonate you. This all-too-frequent occurrence describes the broken Circle of Identity. Yes, tools among the likes of Apple’s Face ID are incredibly handy, but their biggest misgiving is that they are independent of most account registration that is needed for down the line identity management and account security.
Mere decades ago, the process of identity verification was no more complex than being there in the flesh to do it. For anything along the lines of enrolling in banking services or completing an onboarding background check, an individual would need to pay a visit to an in-person office in order for the institution to ensure that they themselves matched the provided forms of identification.
Today, all of this is much harder to manage, considering the many issues surrounding data privacy, the dependence on remote processes of identity verification and the demand for instantaneous services. But with reimagined privacy-preserving infrastructures, it is possible to close the Circle of Identity without sacrificing the convenience of the digitally-reliant world we live in. Managing your bank account can happen without the threat of a cyberattack or data breach, but only if systems are designed with the end to end user journey in mind. With cloud-based decentralized biometrics, your banking institution will be able to verify that you are the person that you claim to be. There isn’t any need for you to answer silly questions that ask you what your mother’s maiden is or for the name of the street you grew up on––information that can be easily stolen, sold, and/or exchanged on the dark web. The ultimate key to your rightful access is you; and you are a powerful, unstealable password.
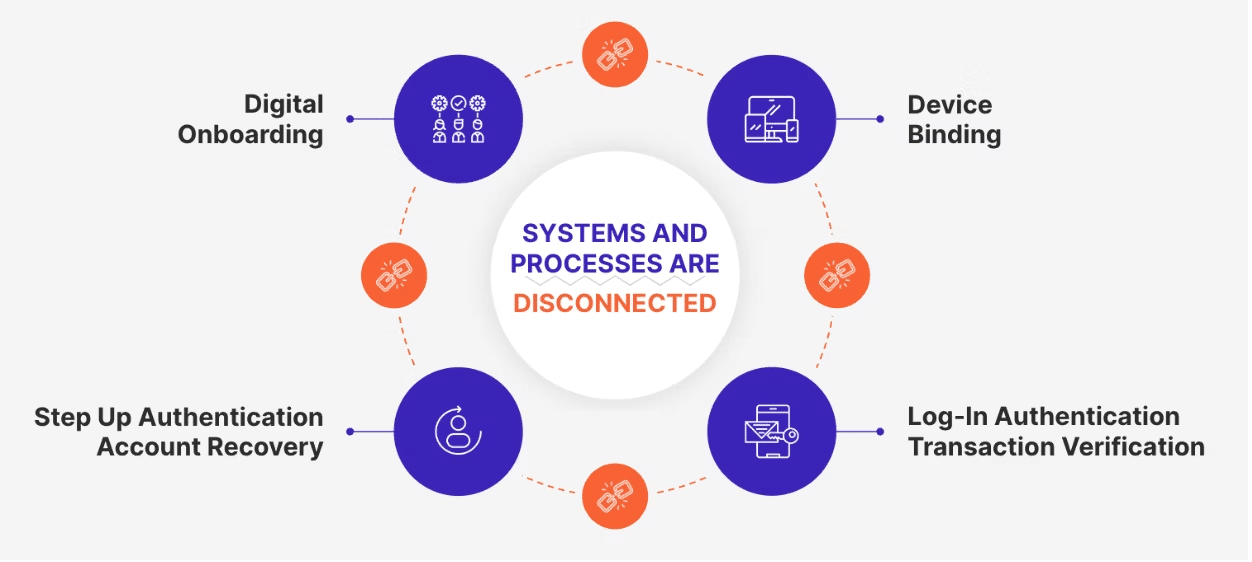
A closed Circle of Identity works like this: Selfies and other data collected at account registration are registered as the means of verifying identity down the line. Any device becomes linked and provisioned to that registration along with the user’s biometric. A call to the call center or the purchase of a new device leverages the biometric that is also linked to the original registration––the same goes for reprovisioning private keys and digital assets.
The breakthrough privacy-by-design aspect ensures that the personal data including the biometrics is not stored in any central honeypot. New frameworks also ensure that data is not recompiled or reverse engineered to regenerate the original record and that the consumer remains in control over when and how their personal data is used. There is no single owner of the data and there is nothing for a hacker to find or steal. In a world where remote processes heighten the risk for security breaches, leveraging these new capabilities and closing the Circle of Identity is key if we have any hope of stemming the tide around identity theft and fraud.
